Security Testing
Tomaso Vasella
This article aims to give a short introduction into Software Defined Radio (SDR), an interesting field for everyone who likes radio transmission, hardware hacking and just accessing things you normally can’t access. At the end of this introduction, you should be able to get your antenna up and running, know the good resources for further research and use available tools to track airplanes.
Radio signals were traditionally received and processed using hardware components (antenna, filter, demodulator, amplifier etc.). Software defined radio aims to process signals in software rather than hardware. The antenna delivers a raw signal to the software which then demodulates it, and further processes it. Said processing can be either readily available or developed independently.
On the USENIX Security Symposium 2009, two researches of the Ecole Polytechnique Federale de Lausanne (EPFL), Martin Vuagnoux and Sylvain Pasini, presented their research on Compromising Electromagnetic Emanations of Wired and Wireless Keyboards. They were able to recover full or partial keystrokes with the highest success rate (95%) on old PS/2 keyboards, but also USB and wireless keyboards are affected. The most impressive thing about their research, apart from the fact that such an attack is possible, is the distance: Their attack compromised sensitive information over a distance of 20 meters.
The researchers came up with four different forms for discovering and exploiting emanations and were also able to distinguish keystrokes from multiple keyboards which were used at the same time.
Compromising Electromagnetic Emanations of Keyboards Experiment 2/2 from Martin Vuagnoux on Vimeo.
Another project recently published by two researchers of the Ben-Gurion University of the Negev, Mordechai Guri and Yuval Elovici, called AirHopper, uses an Android smartphone and the internal FM radio (headphones as antenna) to detect electromagnetic emissions that are generated by keystrokes on a target machine.
The scenario is based on three elements:
Hostile code is installed on the target machine and smartphone, a C&C channel is established to the smartphone and its FM radio is used for monitoring the radio channel in order to detect and decode information on the smartphone.
The hostile code on the target machine creates an FM audio signal using the display adapter. This signal can either be modulated by Dual Tone Multi-Frequeny (DTMF) or Audio Frequency-Shift Keying (A-FSK) onto the carrier frequency.
These research projects are very interesting, because computer environments are quite often shielded. But the quality of these shields may vary for different computer hardware. Let’s think about a scenario where the EPFL results are used to identify keystrokes of a Point-of-Sale terminal that is used to enter debit card PIN in a convenience store. Or another scenario, where skimmers would like to reduce the risk of exposure while skimming ATM card details and PIN. In both scenarios the magnetic stripe of the debit card has to be copied, but the PIN recording can be done over a distance.
Sniffing keystrokes is one thing and certainly a very interesting topic of research. However, for someone starting with this it might just be the little bit of motivation needed to purchase an antenna and setup a system to get going. There are multiple websites (e.g.: rtl-sdr.com, OsmoSDR, radio.linux.org.au and rtl-sdr on OsmoSDR) which have lists of existing projects that give almost off-the-shelf solutions.
Note: Please check for any and all legal issues that might arise in your location. You may not be allowed to do everything you want in your location, this especially applies for any and all projects that transmit signals.
Hardware that forwards a raw signal to process in software is needed and which has a supported chipset. The OSmocom website is a good source to get started and even mentions some capable hardware. The Realtek RTL2832U is a cheap DVB-T demodulator that allows raw I/O samples to be transferred to the host. The second factor to focus on is the tuner. A tuner with a large frequency range gives the users the opportunity to use it for many different projects. The tuner in the hardware used for this article is the Rafael Micro R820T and serves a frequency spectrum from 24 – 1766 MHz.
Software exists and, depending on the project, some more packages are required. The host system for this article is a 32bit Fedora Linux. And for the beginning the focus is on retrieving Automatic Dependent Surveillance Broadcast Data transmitted by airplanes.
ADS-B stands for Automatic Dependent Surveillance-Broadcast which is a system to track airplane positions. If an airplane has the system activated, it will periodically send information about its position, altitude, speed and more. The messages containing all this information are sent as a broadcast and as such it is receivable by everyone. Flight tracking websites such as www.flightradar24.com use this information to deliver a web service for flight tracking.
We are going to use Dump1090, a Mode S decoder for RTLSDR devices to receive and decode ADS-B traffic. The program can be used simply on command line or offers a map-based visualization.
The following command installs the rtl-sdr and other libraries used by Dump1090.
yum install rtl-sdr-devel.i686 rtl-sdr.i686 libusbx-devel.i686
The installation from official Fedora repositories is the easiest way. Another option is the git checkout, the repository.
Next is getting the source for Dump1090, either via wget or again by git checkout:
wget https://github.com/antirez/dump1090/archive/master.zip
The compilation is straight forward:
Once the installation is done, check the software for functionality.
[root@localhost]# rtl_test -t Found 1 device(s): 0: ezcap USB 2.0 DVB-T/DAB/FM dongleUsing device 0: ezcap USB 2.0 DVB-T/DAB/FM dongle Detached kernel driver Found Rafael Micro R820T tuner Supported gain values (29): 0.0 0.9 1.4 2.7 3.7 7.7 8.7 12.5 14.4 15.7 16.6 19.7 20.7 22.9 25.4 28.0 29.7 32.8 33.8 36.4 37.2 38.6 40.2 42.1 43.4 43.9 44.5 48.0 49.6 No E4000 tuner found, aborting. Reattached kernel driver
The output displays that the DVB-T dongle was found and that a Rafael Micro R820T tuner is present. The next step is to run Dump1090 and see what airplanes are transmitting.
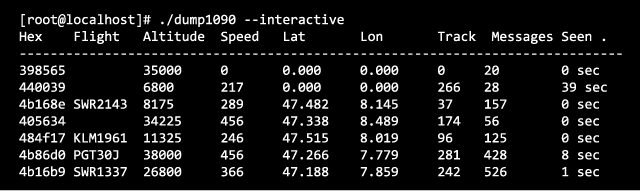
Start Dump1090 with the following command and browse to http://127.0.0.1:8080 in order to see the planes on a map.
./dump1090 --interactive --net
Software Defined Radio has a great variety of usecases. ADS-B related projects are great for getting started in this field. There is plenty of software and information available. Other projects can be used to for demonstration pruposes (e.g. GSM sniffing). With the right equipment such as the HackRF One unknown raw transmission data can be analyzed and reverse engineered. A potential project could be to read and resend radio transmitting keys (e.g. car keys, garage openers etc.).
We are going to monitor the digital underground for you!

Tomaso Vasella

Eric Maurer

Marius Elmiger

Eric Maurer
Our experts will get in contact with you!