Specific Criticism of CVSS4
Marc Ruef

DRM stands for digital rights management. It describes a way to define the usage rights for a digital component and implement them in a technical sense. The public first became aware of DRM when the music industry used it in an attempt to restrict the ability to copy audio CDs. Much to the annoyance of customers, however, this copy protection mechanism was incompatible with older playback devices. A similar effect was seen with downloadable music, which is also being offered increasingly without DRM. The music industry has since come to the realization that, instead of restricting the user, the best way to prevent piracy is by offering high-quality, technologically convenient products at fair prices.
The main field of application for digital rights management has changed in recent years. In the area of applied computer security, the aim of DRM is to minimize misuse of data and software among legitimate and illegitimate users.
In the past, rights management has focused on file objects. A file or directory is assigned an owner, who can then set the access rights for it. A distinction is usually made between owner, member of the same user group, and other users. The three possible actions are read, write and execute. Below is an example of this granular rights assignment within the context of a software development project, in the form typically seen in Unix-like environments:
| User group | Read | Write | Execute |
|---|---|---|---|
| Owner | x | x | x |
| Developer | x | x | - |
| Software test | - | - | x |
| Code audit | x | - | - |
| Software audit | x | - | x |
| Other | - | - | - |
The available possibilities are clearly limited. Although the new enhancements (e.g. sticky bit) have provided a little more flexibility, they have not managed to address the current needs. The aim is to be able to define the file rights for all possible actions and all systems.
RMS stands for rights management system. RMS is a framework that makes the additional features offered by DRM available in an operating system.
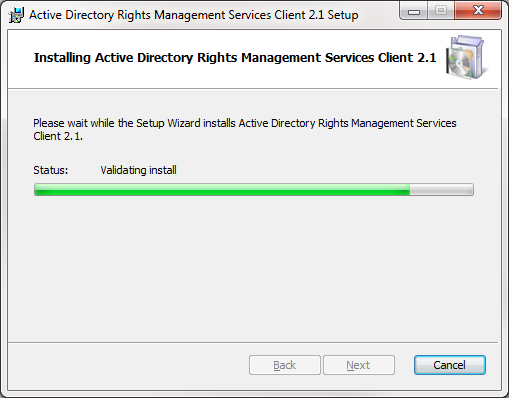
One of the biggest and most promising RMS implementations is provided by Microsoft. It is now referred to as AD RMS (Active Directory Rights Management Services). The RMS client has actually been part of the operating system since Windows Vista and Server 2008. The earlier versions Windows XP, 2000 and Server 2003 can be upgraded. However, administrators and companies have only started taking it seriously in terms of maturity and stability since Windows 8 and Server 2012. With Windows 10 and the 2016 range of Microsoft products, the possibilities are being promoted quite aggressively.
RMS introduces a number of granular configuration options, which also allow rights to be revoked after a document has been shared, for example. These include:
This gives rise to new possibilities. The following example illustrates the different requirements that could be applied to an Excel spreadsheet:
| User group | View | Change | Copy | Save | Automat. | Full | |
|---|---|---|---|---|---|---|---|
| Owner | x | x | x | x | x | x | x |
| Data typist | x | x | x | - | x | - | - |
| VBA developer | x | x | x | - | x | x | - |
| Software audit | x | - | x | x | x | x | - |
| Revision | x | - | x | x | x | - | - |
| Other | - | - | - | - | - | - | - |
Depending on the document type and the client software, this check can open up even more possibilities. For example, sorting and filtering is not possible in read-only Excel documents. However, with the help of a dedicated template, initially conflicting requirements can be met.
Many of the components used in the business domain now support RMS. These include Office, Exchange, SharePoint, Skype for Business and XPS. Integration is largely transparent and therefore fairly convenient.
In the 1990s, Microsoft was not seen as a particularly open company. It fought against open source solutions – Linux in particular – on both an ideological and economic front. The company’s philosophy has changed somewhat since then, a good example being the portability of Microsoft RMS. Alternative operating systems such as Linux and Apple OS X are just as well-supported as the Android, iOS and Blackberry mobile platforms.
This interoperability and portability makes a considerable contribution to the success of the Microsoft solution. Rights for a Word document that have been granted in Office 365 in a Windows environment, for example, will continue to apply after the document has been sent by Gmail and opened on an Apple system.
Microsoft provides a free SDK (software development kit), which allows developers of third-party software programs to ensure compatibility with the system. These include the now well-known Foxit Reader and GigaTrust.
RMS combines a range of different technologies to enable the implementation of rights. To grant access rights for a file via RMS, the client must first connect to an RMS server. This process must be performed separately for each file. The licensing server first checks the credentials and determines the user’s access rights by consulting Active Directory (AD). The content of the processed document is not sent.
In the next step, an author can then configure the required settings under Permissions. These are returned by the publishing server and can be saved together with the file.
The file is then encrypted by the RMS using the public key method. The owner will still be able to view it. At the same time, however, the permissions are set for the other users as well.
If the file is now shared and a user wants to process it (open, edit, copy, etc.), their client first contacts the licensing server again, which checks their credentials and access rights. If the user has the necessary privileges, they can access the file. Otherwise, they will not be able to process it.
Three aspects have a major influence on the success of rights management:
If a document should only be read by the Finance user group, but the group also contains external users, this will inevitably lead to a privilege escalation. Such misunderstandings can only be prevented by managing the users and their group affiliations in a consistent way. It requires a solid process for establishing users and their rights, as well as regular auditing of granted rights and automatic revoking of rights when the user changes roles.
The aim of an authorization concept is to govern which users and user groups are allowed to access which objects. This involves specifying the requirements for granting and revoking access rights. Logic errors at this level can lead to problems during implementation. Having too many user groups is just as obstructive as having object classes that are too generic. It is important to strike a balance between granularity and simplicity.
Last but not least, the technical implementation of the RMS must be solid. This not only includes the installation of the appropriate servers and clients, but also their underlying configuration. Errors at this level will make the entire system vulnerable. A technical audit combined with a config review can help to avoid such pitfalls.
An error in one of these areas can lead to undesirable privilege escalations. Under certain circumstances, a user may be able to copy data that should not even be copyable.
This poses an additional risk associated with multi-threading and graphical user interfaces: there are a number of ways to perform the same action, and addressing them all can be very difficult.
In the case of a copying restriction, the client will usually apply it to screenshots as well, not just to the copy & paste function. However, it may still be possible to generate a print preview of the screenshot. Such multi-layer methods of attack are very common in the Citrix environment. In Microsoft’s in-house implementation, every effort is made to avoid such pitfalls. For example, during a screen-share on Skype for Business, all RMS-protected content is hidden.
DRM was developed as a tool for rights holders to prevent their content from being copied without permission. It has caused controversy on both a technical and a social level, to the extent that many music providers now choose not to use DRM.
However, the underlying idea can also be regarded as an enhancement of conventional rights management for files. RMS provides a framework that makes these additional possibilities available across all systems. The widespread and highly stable Microsoft RMS is making a splash in this field. Thanks to its interoperability and portability, the benefits can also be experienced on alternative systems and mobile platforms.
It typically allows viewing and editing restrictions to be set for files, but copying and saving rights can also be addressed. This granularity makes it more flexible, allowing it to meet the current requirements.
In order for DRM/RMS to be successful, various aspects need to be taken into consideration: user management needs to be consistent, and the access rights must be formally defined and implemented in a technical sense. Carelessness or errors in these areas can lead to privilege escalations and, thus, misuse.
Modern DRM/RMS is still in its infancy. There have only been a handful of major installations worldwide – and not until fairly recently. Time will tell whether the current threats to information security can be adequately addressed with this approach. However, we can generally assume that it will form the basis for the next generation of rights management.
Our experts will get in contact with you!

Marc Ruef

Marc Ruef

Marc Ruef

Marc Ruef
Our experts will get in contact with you!