Transition to OpenSearch
Rocco Gagliardi
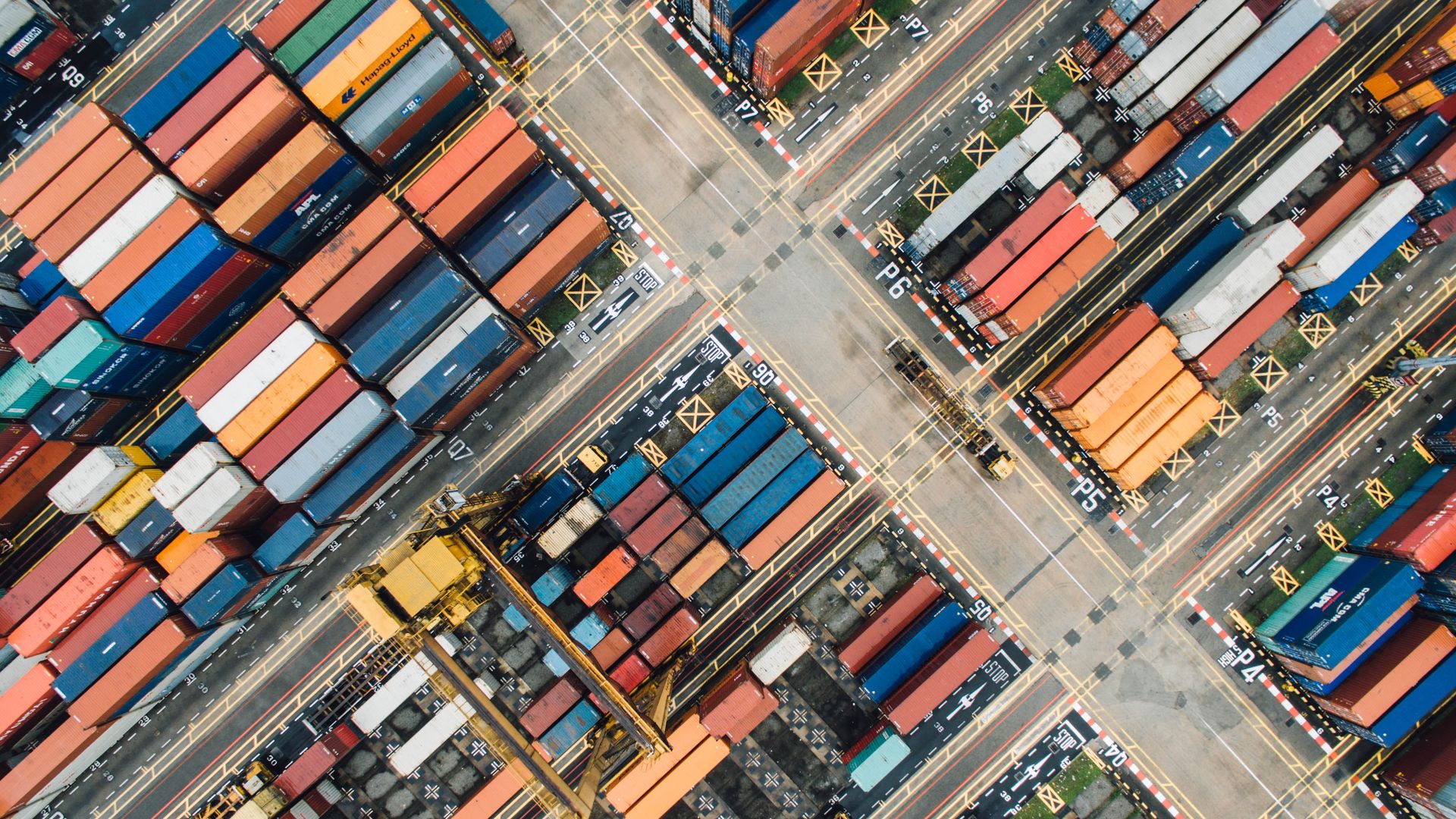
Container, as defined in the dictionary, is an object that can hold something. Extending its meaning: a place where some correlated items can be stored or move together; a separator of things; a constrain for the contained things.
Starting in 1982 with chroot, to BSD-jails, Solaris Containers, LXC, OpenVZ, and Docker, container systems try to keep something isolated from the host system, to keep related things together, to limit the resources a thing can utilize: all focusing and prioritizing different aspects.
This class of technologies is a so called OS-Virtualization technology, to distinguish them from the Full-Virtualization (Type-One: Hyper-visor on bare metal like XEN, ESXi, KVM; Type-Two: Hyper-visor on standard kernel, like VMware Workstation, VirtualBox, QEMU).
Full-virtualization:
Guest process ---\ Guest process -----> Guest OS ----> Host OS ----> Hardware Guest process ---/
OS-virtualization:
Guest process ---\ Guest process --------------------> Host OS ----> Hardware Guest process ---/
Containers are so popular because they are very useful, as example:
They try to resolve a long annoying and costly problem: easier the application life cycle, from the development to the decommissioning. This was the primary goal of Docker in its infancy, regardless to security.
During the last years of the last decade, the advent of hardware virtualization caused a large offer of PaaS, essentially cutting expenses down, that enormously expanded The Cloud. A company called dotCloud was dealing with Linux containers, and developed a framework, released in 2013 as an Open Source project called Docker.
Docker is not Docker. Up to version 1.10, Docker was running on LXC container technologies, with all the downsides. In the spring of 2014, Docker rolled out a new version: they changed from utilizing LXC to libcontainer, a library completely written in Golang and explicitly designed for containers. The library directly manages syscalls and controls the implementation of long awaited security features: Docker now supports – out of the box – namespaces, control groups, capabilities, apparmor profiles, network interfaces and firewalling rules – all in a consistent and predictable way, and without depending on LXC. This improves the isolation of Docker from the side-effects introduced across versions and distributions of LXC.
Today, Docker is not only a daemon, but contains Docker Hub, Registry, Swarm, Compose and diverse supporting tools, like Docker Notary for trusted images, and Docker Machine for provisioning. Look at Docker Security for more information.
The impact of Docker in the next years will still grow; aside the official 64-bit Linux, clients are ready to use on many platforms (Linux, Windows, macOS, FreeBSD), even Microsoft Windows is including support for Docker, and don’t forget the support in IoT world! For additional information, I strongly suggest to take a look at DockerCon 2016 – conferences
Like any technology, containers suffer from some problems but also offer some benefits. On the weaknesses side, we can summarize:
On the benefit side, we can list:
New technology poses new risks; to deal with them, we need to start from the threats the OS-Virtualization introduces in our infrastructure. Some of them are container specific, others are just classic threats:
CAP_SYS_ADMIN capability may lead to guest escaping and host manipulation; (2) Insecure default configuration: defaults are normally trusted, but in many cases they are open; a classic example is the CAP_NET_RAW capability, that can be easily used to perform network attacks; (3) Misconfiguration or weak configuration of networks of procfs or sysfs may facilitate a large range of attacks against the host system.We are the Container. Your physical and virtual distinctiveness will be added to our own. Resistance is futile.
OS-virtualization isn’t really a new technology, but in the last years has been adopted by a very large number of companies, and the number is still growing rapidly.
Docker, in particular, is spreading across infrastructure because it is a great help for operators in application maintenance. At the same time, it is not always clear enough where the limitations or the problems of these technologies lies and how can they be mitigated or controlled. In this article, we recapitulated the key points of the technology and identified some attack scenarios.
Our experts will get in contact with you!

Rocco Gagliardi

Rocco Gagliardi

Rocco Gagliardi

Rocco Gagliardi
Our experts will get in contact with you!