Specific Criticism of CVSS4
Marc Ruef
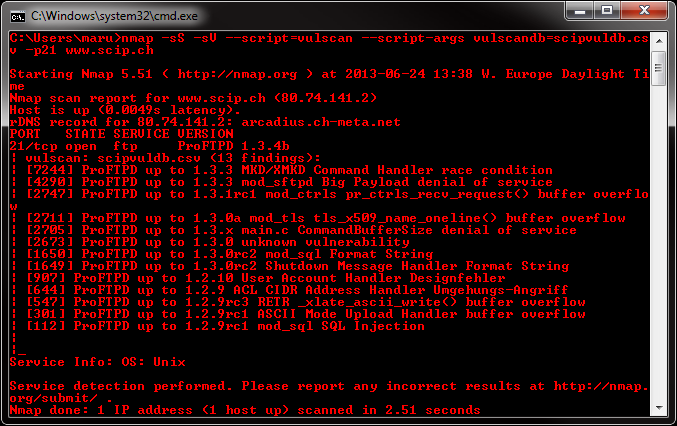
Vulscan is a module which enhances nmap to a vulnerability scanner. The nmap option -sV enables version detection per service which is used to determine potential flaws according to the identified product. The data is looked up in an offline version of different vulnerability databases.
Please download the files and install them into the following folder of your Nmap installation:
Nmap\scripts\vulscan\*
To initiate a simple vulnerability scan you have to run the following minimal command:
nmap -sV --script=vulscan www.example.com
There are the following pre-installed databases available at the moment:
| File | URL | Remarks |
|---|---|---|
scipvuldb.csv | scip.ch/en/?vuldb | – |
cve.csv | cve.mitre.org | – |
osvdb.csv | osvdb.org | outdated, 02/03/2011) |
securityfocus.csv | securityfocus.com/bid/ | – |
| | | usage not permitted |
securitytracker.csv | securitytracker.com | – |
If you don’t use the single database mode, all of the available default databases are used.
You may execute vulscan with the following argument to use a single database:
--script-args "vulscandb=your_own_database"
It is also possible to create and reference your own databases. This requires to create a database file, which has the following structure:
<id>;<title>
Just execute vulscan like you would by refering to one of the pre-delivered databases. Feel free to share your own database and vulnerability connection with me, to add it to the official repository.
If you want to upgrade your database, go to the scip web site and download the current entries:
Copy the full list into the existing database:
/vulscan/scipvuldb.csv
The interactive mode helps you to override version detection results for every port. Use the following argument to enable the interactive mode:
--script-args "vulscaninteractive=1"
All matching results are printed one line. The default layout for this is:
[{id}] {title}\nYou may enforce your own report structure by using the following argument:
--script-args "vulscanoutput='{id} - Title: {title} ({matches})\n'"Supported are the following elements for a dynamic report template:
| Element | Description |
|---|---|
| {id} | ID of the vulnerability |
| {title} | Title of the vulnerability |
| {matches} | Count of matches |
| \n | Newline |
| \t | Tab |
Keep in mind that this kind of derivative vulnerability scanning heavily relies on the confidence of the version detection of nmap, the amount of documented vulnerebilities and the accuracy of pattern matching. The existence of potential flaws is not verified with additional scanning nor exploiting techniques.
Unfortunately, I have received an email today by representatives of Secunia. They do not allow me to include any references to Secunia advisories. This is why I had to exclude the Secunia vulnerbilities in secunia.csv from the current release 1.0.
Our experts will get in contact with you!

Marc Ruef

Marc Ruef

Marc Ruef

Marc Ruef
Our experts will get in contact with you!