Security Testing
Tomaso Vasella

I’m generally not very surprised about how long I’ve been working in information security. I can’t help but notice that times do indeed change, even if it’s just ten years. In 2005, I published an article on ARP Spoofing in Swiss IT-magazine itbusiness which still came out in print back then. I admit, the subject of ARP Spoofing wasn’t cutting edge back then, but today it’s definitely old news. If anything, the topic comes up out of nostalgia and not because people are actually worried about the effects of local man-in-the-middle attacks. Back then, information security was a topic that was interesting pretty much exclusively to companies. Today, in the age where smartphones are always online and the age of the Internet of Things dawns, it’s a topic that everybody must think about.
Therefore, it’s important that people in our business escape the sometimes cynical bubble of the Infosec Community and help the public. I was allowed to speak at the Zürich edition of the series of presentations called Ignite. In my presentation that, according to Ignite rules, wasn’t allowed to exceed five minutes, I presented a dozen simple security tricks for users. They’re simple measures that can be implemented within five minutes and that noticeably raise personal digital security.

You probably know Two-Factor-Authentication from your e-banking, but this is pretty cool for email because your inbox is a pretty high-risk target. Think about it: Somebody could reset most of your passwords using your email account by using the I forgot my password function. So adding Google Authenticator is a smart choice and you can still define your home computer as trusted, so when you’re using it, it won’t ask you for a code everytime. Don’t forget to set up a backup number, so in case you ever lose your phone, you can log in by getting the code in a call or text message. You can also use Google Authenticator with other apps, for example Dropbox.

That company policy that requires you to change your password every two weeks, asking you to memorize another new string of at least eight numbers, letters and special characters is nonsense. Why? Because it tempts people to write down passwords, which is worse than having a password for a longer time. But still, changing your important passwords now and then does make sense. If you are using a Password Manager (see below) it’s very easy anyway, otherwise just pick one critical service and set a new one.
Web Browsers have taken some significant steps to becoming trusted platforms over the past years, but they’re still not perfect. For example, certain types of attacks can try to exploit the fact that you are logged in into another website, for example your e-banking or Facebook. Using a dedicated browser for your regular browsing and a special one for important, personal things can help. You can draw the line wherever you want, but I know a lot of people that like to do everything to do with finances, taxes and similar stuff close to their bank account and identity in a separate browser.

While I understand that tracking is an important aspect of advertising and market research, I am not too fond of actually being tracked while surfing. There is a very neat plugin called Ghostery that will show and, if you want, block any tracking service active on a website you are visiting. Please be aware that, by default, Ghostery only displays what tracking services are being utilized. If you want it to go into full block-mode, you have to activate that feature in the settings.
Losing your phone sucks. Finding it is pretty cool and with most modern systems, you can actually do that. Both Google’s Android and Apple’s iOS have functions to find the last known location of your phone, to lock it, make it ring or wipe all data on it. Obviously, this can be prevented by a thief under certain circumstances, but in some cases it actually really helps to at least prevent someone from going through all your personal stuff in a pinch. Especially if your phone has not been stolen, but was just misplaced, this feature is a lifesaver.
Passwords are an imperfect concept: You shouldn’t re-use them. They should be complex enough not to be guessable. So you need a plethora of complex platforms and for someone like me, who has trouble remembering everything to get while grocery shopping, that can be a problem. A password manager solves that problem for you by only requiring one master password and managing all of your real passwords encrypted until you enter that one. For personal usage, I like LastPass, but if you’re not keen on using a cloud-powered solution, you can also go with the classic, Keepass.
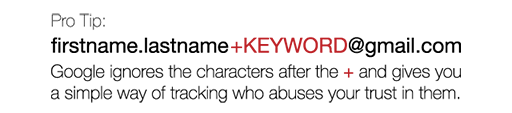
We have to enter our email addresses into registration forms all the time and it’s generally a good idea not to use your main address for some stuff. But no matter what you enter, this little trick for Gmail might prove to be useful: Gmail does not care about dots or everything after a plus-sign in your email address. So if you sign up for a service, you could use the email address firstname.lastname+SCIP@gmail.com and it’d still arrive at your inbox. This has several advantages: You can use different terms after the + to find out who leaked your email to spammers and detect phishing attempts if the keyword isn’t in there, but you can also spot when someone sold your email address to a marketing company.
Facebook and other social networks are notorious for changing privacy options frequently and add new mechanisms that potentially change the visibility of the stuff you share. While you should always assume that things you share on social networks are publicly available, it doesn’t hurt to go through the options now and then do some cleanup. Facebook also provides a function to view your profile through the eyes of another user, which you should do now.
There is really no point in lecturing you about bad passwords for longer than necessary: password: bad. 123456: bad. Your first name: bad. Your last name: bad. Pretty much everything in a dictionary: bad. Good passwords have a certain level of complexity, which makes them harder to guess, but also to remember. This is also the reason Password Managers (see above) are pretty useful. But no matter if you need just one password or a dozen, use something complex. For example, take a whole sentence you can remember and use the first letters of that sentence, mixed with some numbers and add a special char somewhere.

Awareness is such a huge part of security. Knowing how easy it is to do something can really change the way you look at an entire topic. Check out how easy it is to open simple locks and maybe even give it a go yourself. Lockpicking is also practiced as a sport, even here in Switzerland. The club SPASS even does workshops and teaches people about it.
It is an unfortunate reality that most security incidents happen when big services get hacked. Adobe was a prominent example for this. This is also where using the same password everyhwere you go becomes a massive problem. Again: Awareness helps a lot. So on HaveIBeenPwned you can go and check if your username and email shows up in any publicly available dumps of stolen information. If it comes back positive, you might want change your password(s).

The availability of SSL-encrypted web traffic has skyrocketed the past couple of years and a lot of companies have actually adopted a HTTPS-only policy, which is great news. Most sites encourage you to use encrypted HTTPS, but some don’t. But you can use a plugin for your browser like the Electronic Frontier Foundation’s HTTPS Everywhere to make sure you use HTTPS wherever it’s possible.
This list got me a spot on Ignite Zurich where I held a five minute presentation on it. You can watch the video below.
We are going to monitor the digital underground for you!

Tomaso Vasella

Eric Maurer

Marius Elmiger

Eric Maurer
Our experts will get in contact with you!