Reporting and Documenting
Michael Schneider

Imagine a sex toy talking with an application on the phone, adjusting mechanical parameters in accordance with the personal profile stored, or based on FB Likes, or using a playlist of mechanical movements, controlled sounds, lights, and smells, or even a json stream of parameters from a remote controlled application (by another sex toy?) on another continent and you want to test it!
This and other fun objects are called the Internet of Things (IoT). These devices with applications connected to networks, especially the Internet, are often not considered to be computers because of their shape – but they are. Recently it has been popular to test/hack these devices, resulting in the discovery of many nasty vulnerabilities. The OWASP project has suggested an IoT Top Ten, as they have done before for web and mobile applications, to give testers a framework to test in. This article proposes ideas as an extension to the Penetration Testing Execution Standard (PTES) when testing IoT devices.
The reason we look into extending PTES for IoT devices is, that when we test on a regular basis, we usually have one or two technologies and we can define the scope very easily. By contrast IoT devices are not a single technology and not a family reunion of technologies but rather a big collection of different technologies and components. Most devices will have a management interface that could be controlled through a web application, a mobile application or something else. It usually has some kind of network, sometimes wired, sometimes wireless. Only look at those two big topics – we haven’t even touched the actual application.
This article will follow roughly the high level organization of PTES.
The definition of an engagement’s scope is critical to using your time efficiently and not destroying customer relationships. Any input and every output is something worth considering. So when you define the scope of an IoT device additionally think of:
Are all of those in scope? These aspects will be part of the basis of threat modeling.
Intelligence gathering is the foundation of every test. Depending on which level of information gathering, social engineering of the producing and developing companies, it might be worth it. Ask yourself:
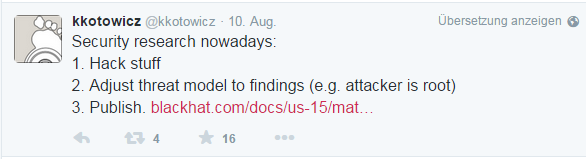
You will need threat modeling. Since we have so many vectors you will have to have threat models for each one of them, and the impact of the findings on each of those is different. Be aware that the following threat model might not be that interesting: “Needs physical access and something you soldered onto the device once you opened it, including removing special screws and maybe heating up the glue so you got access to a seriel interface.”
Also, don’t assume a toaster is safe, because nothing interesting is on it. It’s got a CPU. Sometimes that is all that is wanted.
This chapter needs awareness, that to do vulnerability analysis, you might need the dumped firmware. Think of the entry points the device gives you:
Unless it is whitebox testing, and the vendor gives you all information, you will need to do full traffic analysis.
Exploitation and post-exploitation of IoT devices is fundamentally the same as regular devices. The development of binary exploits is – as always – specific to the architecture of the hardware. Existing exploits for x86 or 64-bit architecture are likely not to work out-of-the-box.
Moreover the operating systems running on such devices are often trimmed, as for example BusyBox, a size-optimized Linux for embedded devices. This will need to be accounted for, when writing a post-exploitation toolchain.
All things considered, the PTES is very comprehensive. As we’ve shown in this article, the situation doesn’t change much when applying PTES to testing IoT devices. The biggest challenge is to keep all entry points in the back of ones mind when developing threat models.
Our experts will get in contact with you!

Michael Schneider

Michael Schneider

Michael Schneider

Michael Schneider
Our experts will get in contact with you!